If there is one cyber threat that still catches well-run businesses off guard, it is business email compromise perth risk. That is because BEC does not always look like a loud technical attack. Often it looks like a normal business process at exactly the wrong moment. A supplier asks for changed bank details. A director requests an urgent payment. A staff member notices a password reset email that they do not remember triggering. A trusted contact sends a message that feels slightly off, but not obviously fake.
That is what makes business email compromise so dangerous. It abuses trust, timing, and routine. The ACSC defines BEC as a form of targeted phishing or spear phishing where criminals use email to scam organisations out of money, goods, or sensitive information. The compromise may involve a fake lookalike domain, a compromised mailbox, or an impersonated sender. In many cases, the attacker succeeds because the request lands inside an ordinary workflow and the business processes it before anyone pauses to verify it.
For Perth businesses with lean finance teams, fast-moving approvals, and heavy email dependence, that risk is very real in 2026. The good news is that BEC is also one of the most practical areas to improve. Stronger email security matters, but process discipline matters just as much.
What business email compromise actually looks like
BEC is not one single scam. It is a family of tactics that all rely on trust.
Common examples include:
- invoice fraud using changed bank details
- impersonation of executives requesting urgent payments
- compromised supplier accounts sending altered invoices
- mailbox compromise used to monitor financial conversations before intervening
- requests for payroll or sensitive employee information
The ACSC’s guidance on protecting against BEC explains that attackers may gain access to legitimate invoices through a compromised vendor email account, then alter the contact or bank details and forward the invoice from that trusted account. That is why these scams can be hard to spot. The formatting, history, and relationship may all appear legitimate.
This is not just a finance-team issue either. Reception staff, operations coordinators, project administrators, and managers can all become part of the attack chain when an attacker is probing for trust, urgency, or process shortcuts.
Why Perth SMBs are especially vulnerable
The vulnerability is not geographical. It is structural.
Many Perth small and medium businesses operate with:
- lean finance teams
- fast approval paths
- regular invoice movement between suppliers and customers
- heavy reliance on Microsoft 365 email
- a mix of in-office and mobile work
- informal verbal assumptions about “what normal looks like”
Those conditions create speed, which is good for business, but speed without verification is exactly what BEC attackers want.
A business may also assume that because it has spam filtering or antivirus, the problem is largely solved. It is not. BEC often bypasses simple technical assumptions because the message itself may not look malicious in the traditional sense. It may simply be persuasive and well-timed.
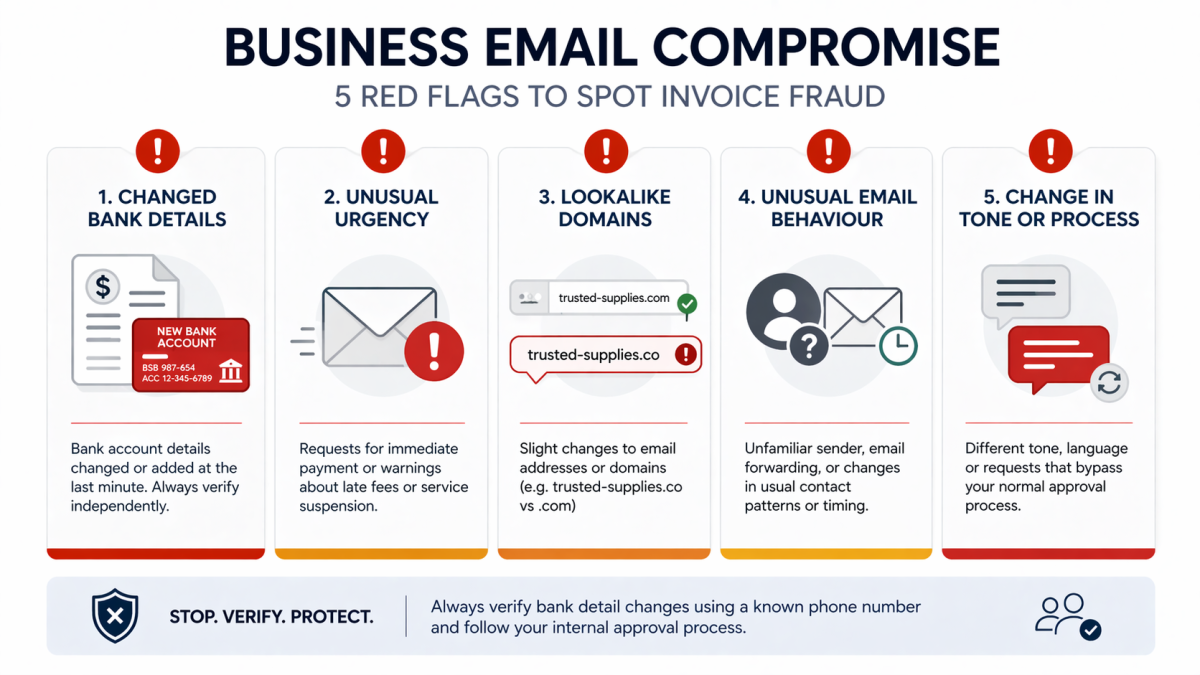
The common red flags
Teams should know the signs that justify a pause.
Requests to change bank details
This is one of the most common warning signs. Any request to change payment details should trigger a separate verification process.
Unusual urgency
Attackers try to create time pressure. They want people to approve, pay, or reply before they think carefully.
Minor domain or address changes
The sender may look legitimate at first glance, but closer inspection may show a misspelt domain or a slightly altered address.
Strange mailbox behavior
The ACSC notes that unusual password resets, deleted emails, or messages moved unexpectedly can be indicators that an email account has been compromised.
Changes in tone or process
An established supplier suddenly asking for a different payment route, an executive requesting secrecy, or a customer contact using unfamiliar phrasing all deserve verification.
The 10 controls that reduce BEC risk
The strongest BEC protection comes from combining people, process, and technical controls.
1. Enforce MFA on email accounts
The ACSC highlights MFA because it makes account takeover harder. Start with the highest-value accounts first:
- executives
- finance staff
- payroll users
- shared operational inboxes
- administrators
2. Protect business domains
Email security includes protecting the domain your business uses. Renewal discipline, registrar security, and sensible controls over who can make changes all matter.
3. Lock down admin privileges
If attackers gain privileged access, the blast radius increases. Restrict admin rights and review them regularly.
4. Use strong approval workflows for payment changes
No bank detail changes should be accepted on email alone. Require a separate callback to a trusted number already on record, not the phone number in the suspicious message.
5. Train staff on real scenarios
Training is most effective when it uses the business’s real workflows. Show finance teams what altered invoices look like. Show operations staff how executive impersonation works. Show everyone how easy it is for a familiar sender name to be misleading.
6. Review mailbox rules and suspicious forwarding
Attackers who compromise a mailbox often create forwarding rules or hide messages. Reviewing mailbox behavior is part of the response posture.
7. Keep devices and email platforms secure
Old endpoints, unmanaged devices, or inconsistent identity controls increase compromise risk. Email security is not separate from endpoint and identity hygiene.
8. Reduce trust in email as a sole authority
This is more cultural than technical. Staff should understand that an email is not proof. It is only one input.
9. Build an incident response playbook
Teams should know exactly what to do if they suspect:
- a mailbox was compromised
- a fraudulent payment was sent
- a supplier account appears hijacked
10. Review and test
Like most security controls, BEC protection weakens when it is assumed rather than checked. Review approval processes, mailbox security, and user awareness regularly.
A practical payment verification workflow
One of the best ways to reduce invoice fraud is to create a simple mandatory process.
When banking details change:
- stop the payment workflow
- verify the request through a separate channel
- call a known contact using an existing number
- record who verified the change
- require a second internal review if the amount is material
This is not bureaucracy for its own sake. It is a control designed for one of the most expensive forms of email fraud.
How a BEC attack often unfolds
Understanding the attack path helps staff spot weak points earlier.
Stage 1: access or impersonation
The attacker either compromises a mailbox or creates a believable impersonation address. At this point the goal is credibility.
Stage 2: observation
If a real mailbox is compromised, the attacker often watches first. They learn who approves invoices, how often suppliers are paid, and which conversations involve money or urgency.
Stage 3: intervention
At the right moment, the attacker inserts a request:
- updated bank details
- urgent payment request
- reissued invoice
- payroll or confidential file request
Because the request is inserted into a legitimate-looking business rhythm, it can feel normal to the recipient.
Stage 4: pressure
The attacker introduces urgency, authority, or embarrassment. They do not want the target to slow down or verify independently.
Stage 5: concealment
If the attacker controls a real mailbox, they may hide messages or create forwarding rules to reduce the chance of detection while the fraud proceeds.
When staff understand this sequence, they become much better at interrupting it.
What to do if you suspect compromise
Speed matters.
If you think a mailbox has been compromised:
- change passwords immediately
- revoke active sessions
- review MFA status
- inspect mailbox rules and forwarding settings
- review recent sign-ins
- check whether external messages were sent from the account
If you think a fraudulent payment has already been made:
- contact your bank immediately
- preserve email records
- identify who approved the payment
- notify impacted stakeholders
- escalate to your IT and cyber response contacts quickly
Even if the business is unsure, it is better to escalate early than to spend hours privately debating whether something looks suspicious enough.
Questions finance and operations leaders should ask each month
BEC resilience improves when leaders ask a few recurring questions:
- Did any supplier banking details change this month, and how were they verified?
- Which finance users still lack strong MFA or secure sign-in controls?
- Were any suspicious email rules, forwarding changes, or login anomalies detected?
- Are shared mailboxes still necessary, and who can access them?
- Have staff seen any near misses involving invoice or impersonation attempts?
These are simple questions, but they keep the risk visible. BEC tends to succeed in businesses where nobody owns the crossover between email security and payment process.
A practical awareness exercise for staff
Staff training becomes more effective when it uses scenarios that look like the business’s real environment. A short monthly drill can go a long way.
For example, send a controlled internal exercise that shows:
- an urgent payment request from a lookalike executive address
- a supplier invoice with changed bank details
- a password reset prompt that the user did not initiate
Then teach the team the exact expected response:
- do not approve or pay
- do not reply with sensitive information
- verify through a trusted secondary channel
- escalate to the right internal contact
This kind of rehearsal is useful because it converts theory into muscle memory. When a real suspicious email arrives, the staff member is less likely to improvise under pressure.
It also makes escalation faster. In a real event, delay is expensive. Staff who already know the internal contact path, the verification rule, and the stop-payment process are much more likely to interrupt the fraud before money moves.
For businesses that want to go one step further, combine awareness drills with short reviews of:
- mailbox rule changes
- high-risk login alerts
- finance process exceptions
- supplier master-data changes
That keeps BEC prevention tied to daily operations instead of leaving it as a once-a-year awareness topic.
The businesses that improve fastest are usually the ones that treat near misses as useful signals. If a staff member spotted a suspicious invoice before payment, that should trigger a quick review of what worked, what nearly failed, and whether any process step still needs tightening.
That kind of disciplined review helps prevention improve over time.
It also strengthens team confidence during future suspicious-payment events.
Why BEC is not “just a staff training issue”
Some businesses reduce the whole problem to user awareness. That is incomplete. Training matters, but so do:
- identity controls
- mailbox security
- approval design
- escalation speed
- managed monitoring
If the finance team is expected to carry the whole burden without technical protection or clear process support, the business is setting them up to fail.
That is why BEC prevention fits naturally inside broader [cyber security services](https://www.royalit.com.au/it-security/cyber-security/). Email security, MFA, device management, domain protection, and incident response planning all reinforce one another.
A 2026 checklist for Perth businesses
If you want a practical starting point, work through this list.
- Enforce MFA on all priority email accounts.
- Review finance and payroll approval processes.
- Document a mandatory callback process for bank detail changes.
- Review shared mailbox access and legacy accounts.
- Check for suspicious mailbox forwarding and hidden rules.
- Train staff using realistic invoice fraud examples.
- Review domain renewal and account ownership.
- Confirm who handles incident escalation and banking contact.
- Test what happens if an executive mailbox is compromised.
- Make BEC a recurring review topic, not a once-a-year awareness slide.
This is manageable work. The challenge is usually not complexity. It is consistency.
How Royal IT can help
Royal IT helps Perth businesses reduce BEC risk by strengthening the technical environment and the human process around it. That can include:
- Microsoft 365 security review
- MFA coverage and identity hardening
- mailbox compromise checks
- suspicious activity review
- payment-process risk advice
- staff guidance and escalation planning
The benefit of local support is that it connects cyber control to the real business workflow. Finance teams do not need abstract cyber language. They need safer approvals, clearer escalation, and systems that are harder to abuse.
If your team has seen suspicious invoices, odd password resets, or near misses involving payment instructions, that is already enough reason to review your exposure. You can [contact Royal IT](https://www.royalit.com.au/contact/) to talk through the next steps.
The bottom line
Business email compromise remains dangerous because it feels normal until the money is gone or the mailbox has been misused for days. That is why the best defence is not one tool. It is a layered operating model:
- strong identity protection
- careful mailbox security
- disciplined financial verification
- trained staff
- fast incident response
Perth SMBs do not need to become cyber specialists to improve here. They do need to stop assuming that a familiar email is enough proof. Once that mindset changes, practical controls become much easier to implement.
FAQ
FAQ: Business Email Compromise Perth
What is business email compromise?
BEC is a scam where criminals use email to impersonate trusted contacts or abuse compromised accounts to steal money, goods, or sensitive information.
Is BEC the same as ordinary spam?
No. It is usually more targeted and relies on trust, timing, and realistic business context.
What is the most important control?
There is no single control, but MFA plus strong payment verification processes are among the highest-value starting points.
Should bank detail changes ever be accepted by email alone?
No. They should always be verified through a separate trusted channel.
Can a managed IT provider help reduce BEC exposure?
Yes. Identity hardening, mailbox review, process advice, and incident support all help reduce risk.